Shenzhen Pinmei / Linklemo A9 Mini Camera with Beken BK7252NQN481 – Photos, Boot Log, Flash Backup
TL;DR
- A Shenzhen Pinmei / Linklemo A9 Mini Wi-Fi camera teardown reveals a budget surveillance device sold with 4K, night-vision, motion-detection, and Xiaomi branding claims.
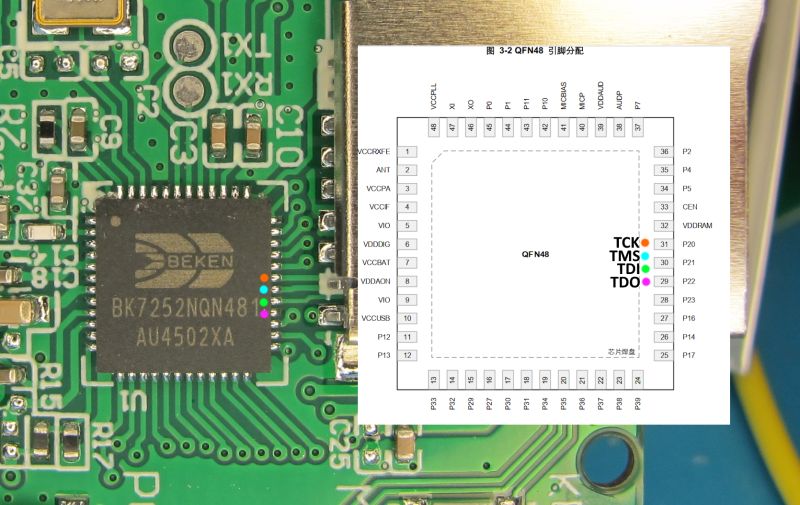
- The internals use a Beken BK7252NQN481, with TX1/RX1 UART access and pads for TDI, TDO, TMS, and TCK for boot-log capture and flash backup.
- Easy Flasher reads the BK7252N in both BK7252 and N modes, BKFIL accepts it too, and the flash reports ID EB6015.
- The 2 MB dump is being prepared for FlashDumps, with a proposed BK7252U/BK7252N split and backups planned under IoT/BK7252N.
- The 4K and Xiaomi sellpoints look dubious, and the PCB text INO-IPC-A9-V2.4 has no found FCC submission.
Generated by the language model.

The ubiquitous A9 Mini Wi-Fi Camera, in its seemingly many forms, is a compact, budget-friendly smart surveillance device, often seen for as low as $1USD as a Welcome Deal on sites like Ali Express. Positioned as a security camera, baby monitor, spycam, camcorder, it is often advertised by sellers as being 4K, having night-vision/infra-red, AI, motion detection. It can usually be said that one or more of these claims is false or at best, exaggerated. The device that is the subject of this post is listed with these "sellpoints" on Ali:
-Xiaomi Mini Camera4k Wireless Wifi Remote Camera4K Ultra Clear Image Quality:Capture every detail with 4K resolution, ensuring clear and vivid footage even in low light.
-WiFi/IP/AP Flexible Connection:Seamless connectivity with multiple modes: WiFi, IP, or AP, for uninterrupted monitoring.
-Intelligent Mobile Detection:High-precision motion sensors trigger alerts, reducing false alarms and enhancing security.
-Portable Design with Magnetic Base:Easily place the camera in any corner with its magnetic base, saving space and ensuring flexibility.
-Long Term Battery Life:Reliable performance with a large capacity battery, ensuring worry-free operation.
I am immediately sceptical about it being 4K and having anything to do with Xiaomi!
My device was sourced from Ali here https://www.aliexpress.com/item/1005008584918966.html

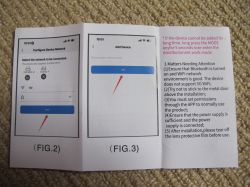
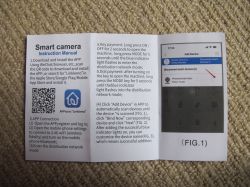
I'll now start by documenting the packaging and device before diving into the internals. Subsequent posts will detail the pairing/app user experience, as well as providing real images and videos created by the device.
The box for this came marked with reference to "Shenzhen Pinmei Technology Co., Ltd".









Inside we see a 2mb BK7252NQN481 - datasheet: https://www.elektroda.com/rtvforum/topic4118348.html#21526095









from TX1 @115200 baud
Code: Text
On one side are pads labelled TDI and TDO (accessible with camera ribbon removed). TMS and TCK are not so obvious.

TCK and TMS are these two:
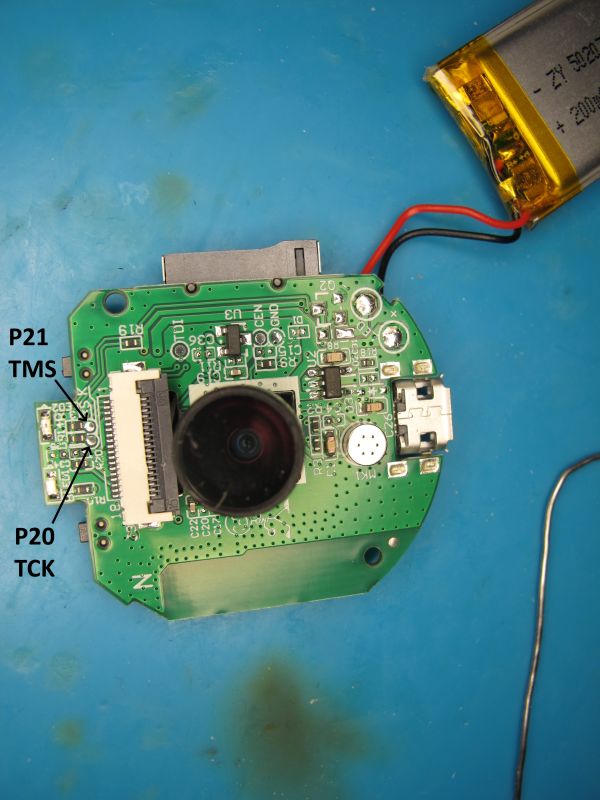
I will later attempt SPI dump using these 4 pads as well as UART backup.
PCB text: INO-IPC-A9-V2.4 - I have not found FCC submissions for this device or company
From RX1/TX1 Easy Flasher reads in BK7252 mode but this skips bootloader. It also reads in N mode which covers the whole 2MB. Maybe BK7252N is more like BK7231N, it also seems to have a romcode like N. Maybe EF needs to have separate BK7252U and BK7252N modes. Maybe EF could have chip detect and it select the right mode if known? BK7252N CHIP_ID = 0x7252a
BKFIL is also happy with BK7252N where it wasn't interested in the older BK7252U.
Code: Text
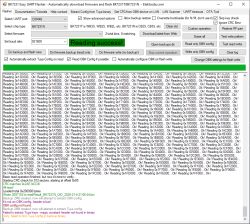
Flash ID is familiar EB6015 and coeff in efuse is 00e46d00 00e46d00 00e46d00 00e46d00
Code: Text
I propose a split of BK7252U and N folders in FlashDumps https://github.com/openshwprojects/FlashDumps/pull/28
If accepted my backups will land in https://github.com/openshwprojects/FlashDumps/tree/main/IoT/BK7252N
that's it for tonight with this cam
Sep 2025. Adding image for device list




Comments
Are you sure that this device is encrypted? This encryption keys looks like the NiceMCU keys, which are invalid because readout is disabled. @insmod ? Is your device working with this exploit (get... [Read more]
not yet analysed dump to see if encryption is used. that's just what was read from efuse. if readout is disallowed isn't the read 00000s rather than an actual key? not yet attempted [Read more]
There are string references, so I guess not encrypted. https://obrazki.elektroda.pl/4216102700_1745310632_thumb.jpg https://obrazki.elektroda.pl/5699160000_1745310638_thumb.jpg I think we... [Read more]
I assumed/hoped so. I'll get working SPI method then confirm by killing 0x0-> Added after 5 [minutes]: I've not looked inside it, but the rom dump was also successful. In flashdumps. [Read more]
Rom mentions BK7238 at 0x18B8, so i guess you would have to try to boot 7238 binaries, and not N. And keys readout is not disabled, since we can get at least something out of them, but addresses were... [Read more]
cool cool. ah yes. did notice this in main flash dump actually https://obrazki.elektroda.pl/9584955000_1745313993_thumb.jpg [Read more]
Maybe you should also try to take a 4M backup? FAL prints that flash length is 4M, even if partitions are configured to 2M [D/FAL] (fal_flash_init:63) Flash device | ... [Read more]
interesting. 0x0-0x400000 result from BKFIL attached. shows repeat at 2mb though https://obrazki.elektroda.pl/6538363600_1745318908_bigthumb.jpg [Read more]
It's the address wrap around I've mentioned recently. This is the way we can read bootloader on BK7231T. BK7231T has read offset 0x0 to 0x11000 protected, but if we add 2MB, then we can both read.... and... [Read more]
xref: accidental post about this cam in other thread re SPI https://www.elektroda.com/rtvforum/viewtopic.php?p=21527527#21527527 [Read more]
Thank you for sharing your work. Is it the same hardware as in the round A9 camera from the thread discussed earlier*? I looked at a picture of one customer on Aliexpress and it looks better than the... [Read more]
And I'm interested in whether it outputs any stream? For 9PLN a nice option to read my analogue water meter, I have an ESP32CAM there but this one so much more convenient because it has a case etc :) [Read more]
@austin007 we've already seen about four variants of these A9s and their batches are not interchangeable with each other (there is either BK7525, or BK7525N, or XF16, or some other chip). On the other... [Read more]
that sample pic looks too good to be an A9 cam though doesn't it? The aspect ratio and wide angle lens isn't something I've seen I don't think for a camera at this level, not my A9s anyway. on the subject... [Read more]
salve_id is in BK code: https://obrazki.elektroda.pl/4020509400_1745441017_thumb.jpg Btw maybe we should add a "camera" tag for Devices List? https://openbekeniot.github.io/webapp/devicesList... [Read more]
sure. there are other platforms missing too though. [Read more]
This also needs to be fixed - there is just one result for "camera" on our site: https://obrazki.elektroda.pl/4604837300_1745478292_thumb.jpg [Read more]
On the subject of the Pinmei A9 BK7252 cam: in pairing mode it broadcasts an AP - the SSID and key for which can be seen in the boot log ssid:LLM_H0A9_06615F key:12345678 https://obrazki.elektroda.pl/9768568200_1745516984_thumb.jpg... [Read more]
Are you able to pair with this app without pairing with cloud? Via access point? Can you provide here the APK file of this app? Maybe we could analyze it. [Read more]