I have a question. I've been trying to make OBK fallover by spamming it with repeated oversized http requests.
Using this:
and with 1.18.253 I get this kind of dropping heap until device reboots, not always, but mostly, especially if clicking about in the gui. This device has MQTT, HA, BL0937 configured.
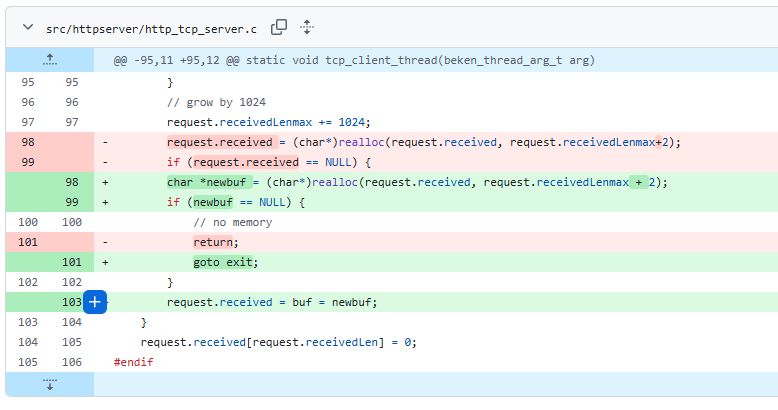
with these changes https://github.com/openshwprojects/OpenBK7231...mpare/main...divadiow:OpenBK7231T_App:tcpleak
I can run the stress-test script over and over with seemingly little effect. (starting HA discovery drops heap to 30k from which it doesn't seem to recover - maybe that's a different issue or to be expected?)
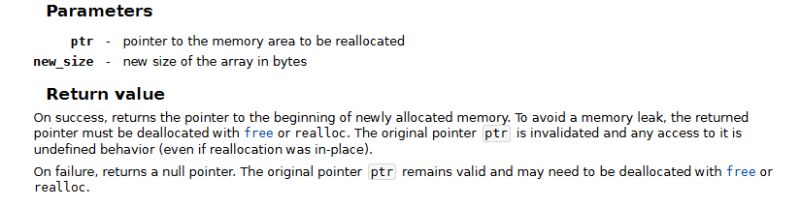
is this a realloc bug?
Using this:
Code: Powershell
Code: Powershell
and with 1.18.253 I get this kind of dropping heap until device reboots, not always, but mostly, especially if clicking about in the gui. This device has MQTT, HA, BL0937 configured.
Code: Text
with these changes https://github.com/openshwprojects/OpenBK7231...mpare/main...divadiow:OpenBK7231T_App:tcpleak
I can run the stress-test script over and over with seemingly little effect. (starting HA discovery drops heap to 30k from which it doesn't seem to recover - maybe that's a different issue or to be expected?)
Code: Text
is this a realloc bug?