Code: Text

Czy wolisz polską wersję strony elektroda?
Nie, dziękuję Przekieruj mnie tam

insmod wrote:same binary crc'ed with old encrypt and 0 0 0 0 flags.


struct fal_partition
{
uint32_t magic_word;
/* partition name */
char name[FAL_DEV_NAME_MAX];
/* flash device name for partition */
char flash_name[FAL_DEV_NAME_MAX];
/* partition offset address on flash device */
long offset;
size_t len;
uint32_t reserved;
};
Quote:starting "01PE"


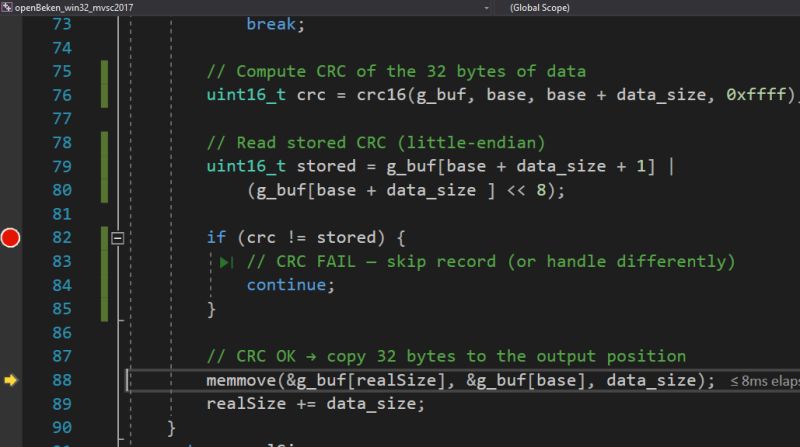
TL;DR: Beken dumps pack a CRC16 every 34 bytes; “Every 32 bytes of data is followed by 2 bytes of crc.” Extract the 01PE table (64‑byte entries) from the first 2 MiB, then parse it to get exact bootloader/app/OTA offsets for OpenBeken. [Elektroda, divadiow, post #21734412]
Why it matters: This lets you decide if you must flash a QIO bootloader or adjust OTA to avoid bricking.
Who this is for: OpenBeken/Tuya/Beken tinkerers who need reliable partition offsets from raw flash dumps so OTA and backups work consistently.
