How do you safely tear down a Sonoff B02-F-A60 retro filament bulb without destroying the RE705-MB-v0.1 module or LED filament wires?
You cannot safely guarantee a non-destructive teardown with the method shown. The metal fitting had to be heated off, and that step broke the LED filament wires as the bulb came apart. 1. Remove the cap slowly after heating the metal shell. 2. Stop before prying deep resin around the PCB. 3. Treat full module extraction as destructive unless you accept wire damage. The thread’s outcome was explicit: the PCB sat under more resin, a metal fitting, and a plastic ring, so further removal destroyed the assembly. [#21520365]





























Comments
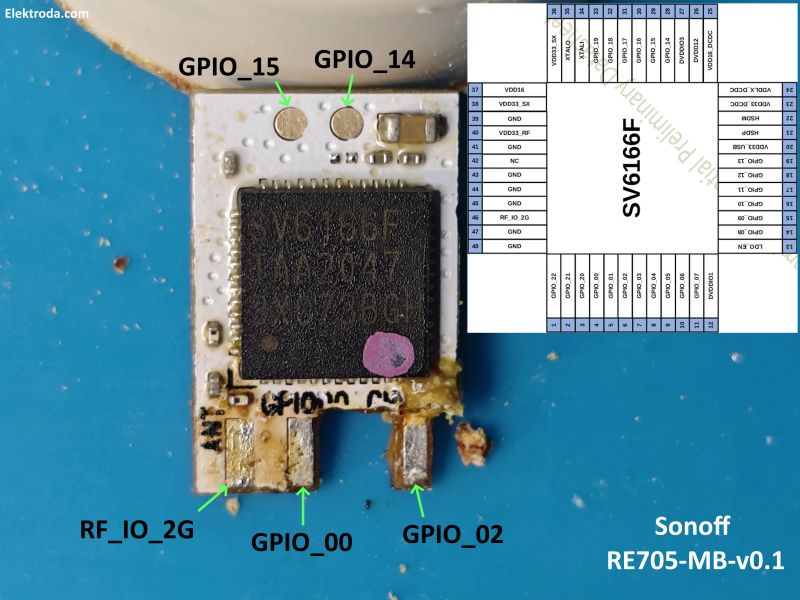
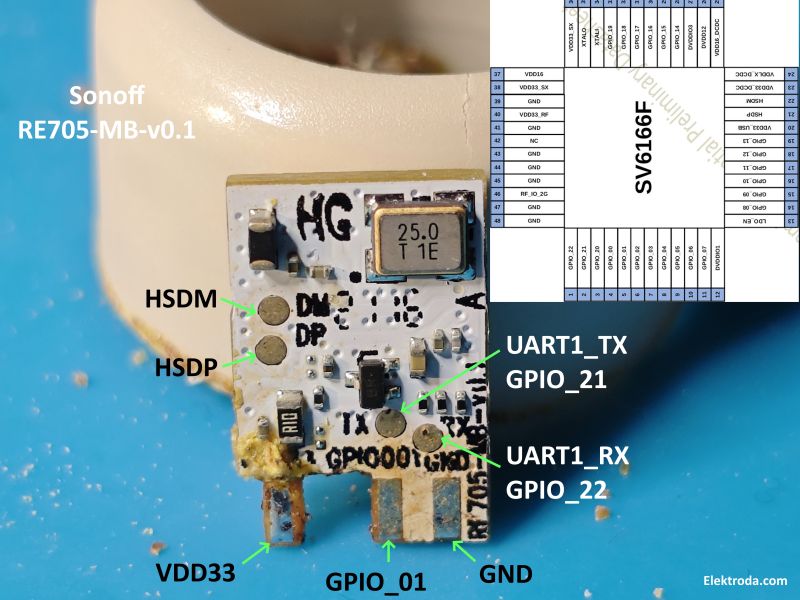
Interesting, I've known Sonoff products for BL602 usage, but not for SV6166F. Still, SV6166F doesn't seem to be new, I see mentions dating back to 2019: https://obrazki.elektroda.pl/9547960700_1744744638_bigthumb.jpg... [Read more]
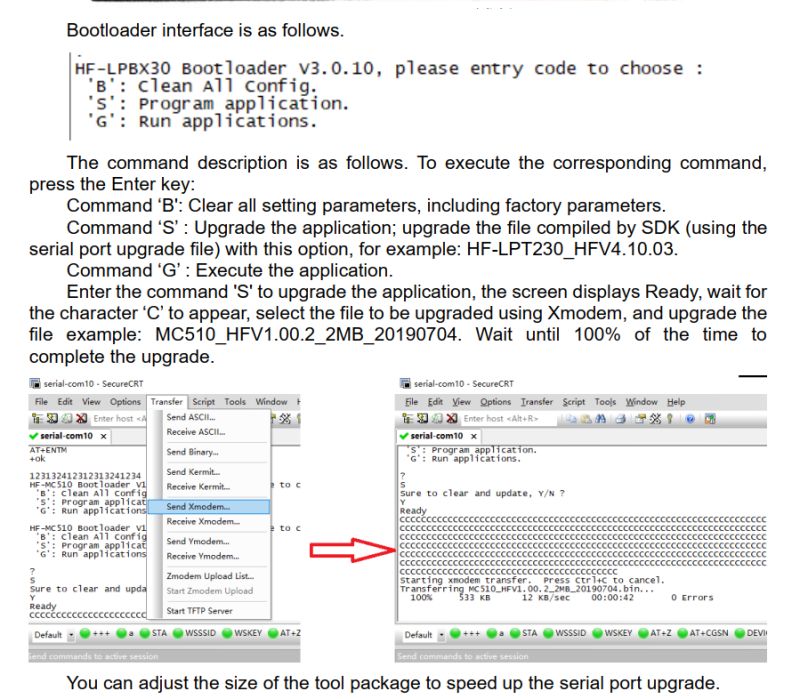
yes indeed. I'm sending various HF firmware to it now to see which boot if any https://obrazki.elektroda.pl/1380039400_1744745156_thumb.jpg Added after 18 [minutes]: these do not h... [Read more]
Do we have any firmware backup from other SV6166F device to try flashing? I can see that SV6166F was also used in Sonoff B02-B-A60 bulbs at some point: https://obrazki.elektroda.pl/5569185700_1744780877_thumb.jpg... [Read more]
regarding your other post https://www.elektroda.com/rtvforum/viewtopic.php?p=21520722#21520722, apologies, there's a little side exploration I tried with this Sonoff module regarding USB that I neglected... [Read more]
Paired with eWeLink app https://obrazki.elektroda.pl/1586757500_1745780578_thumb.jpg https://obrazki.elektroda.pl/2978551400_1745780594_thumb.jpg https://obrazki.elektroda.pl/9068433700_1745780596_thumb.jpg... [Read more]
made this little SV6166F monster. ITEAD firmware in tact on this one. https://obrazki.elektroda.pl/8146653700_1774421094_thumb.jpg exploring flash dump options further. AT response is something... [Read more]