How to recover lost/forgotten MQTT password without creating new MQTT user, without having to reinstall everything again? Why does my password field reads "__**password_not_changed**__" ? Home Assistant Mosquitto broker behaviour has been recently changed. In the past the password was easily accessible via Home Assistant Devices & Services -> MQTT menu, but now it's hidden. That could have taken some users by suprise (including me), so here's a simple solution.
So, in the past, Home Assistant MQTT password used to be easily available in Re-Configure MQTT menu:
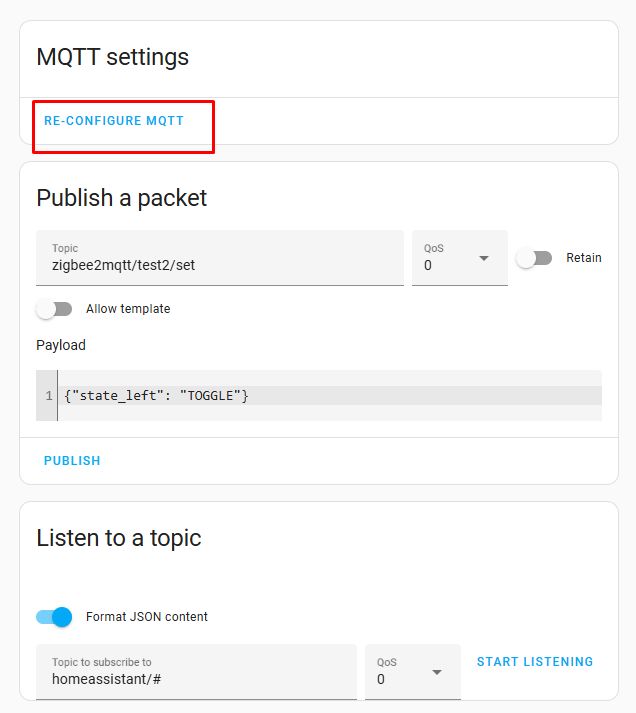
It was easy to display it and copy to your devices to configure them. However, with recent update 2024.5, it is not possible to get password there:
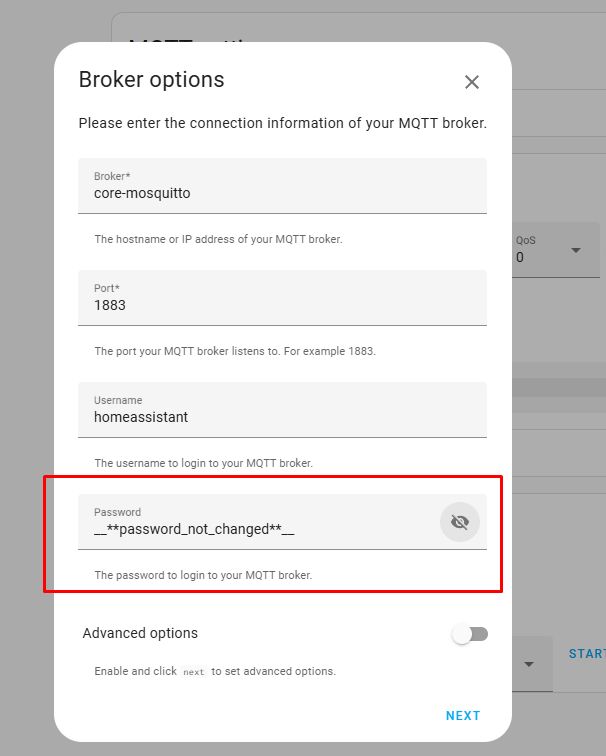
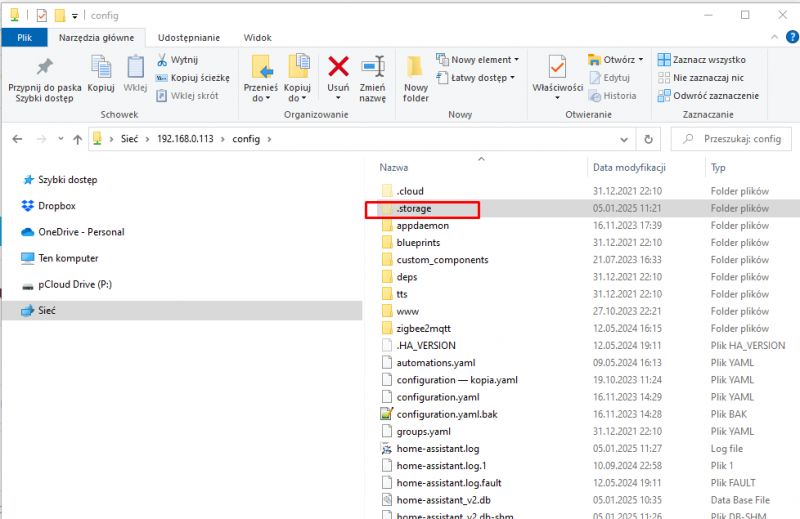
Luckily you can still get it from core.config_entries. For that, you will need to access this file. I have SMB integration already installed, which makes HA access from Windows easy:
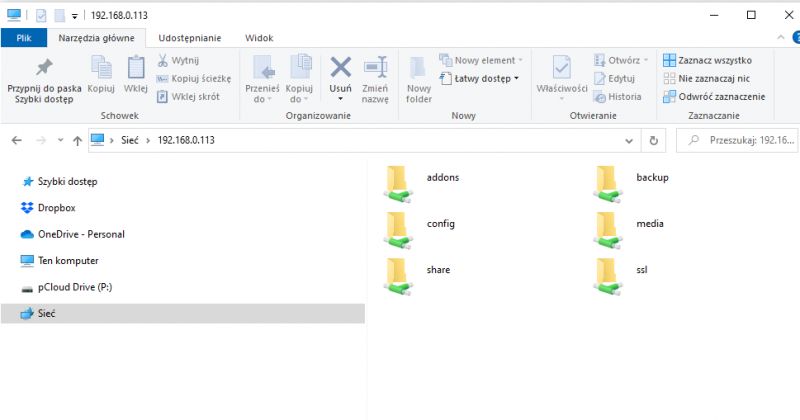
Of course, any other file access solution should also work, it does not have to be the one I used.
Connect to it and navigate to path:
/config/.storage/core.config_entries
Note that .storage directory will be hidden:
Now, open this file with any text editor and search for Mosquitto:
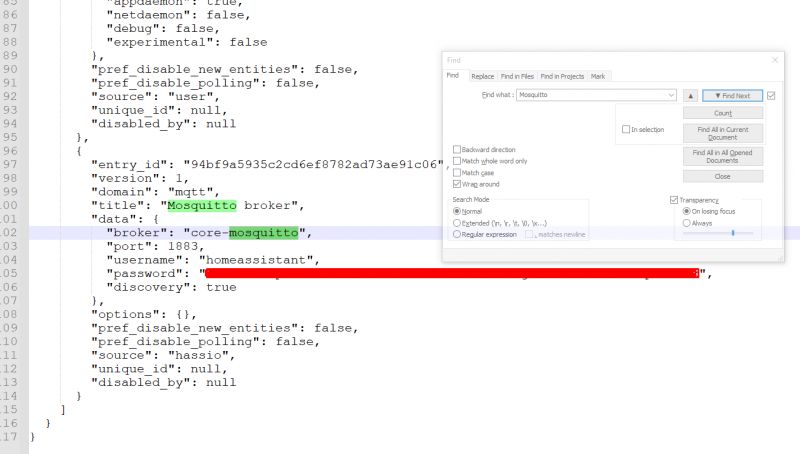
and here it is - this your lost MQTT password!
Of course, do not edit this file, just copy out your password...
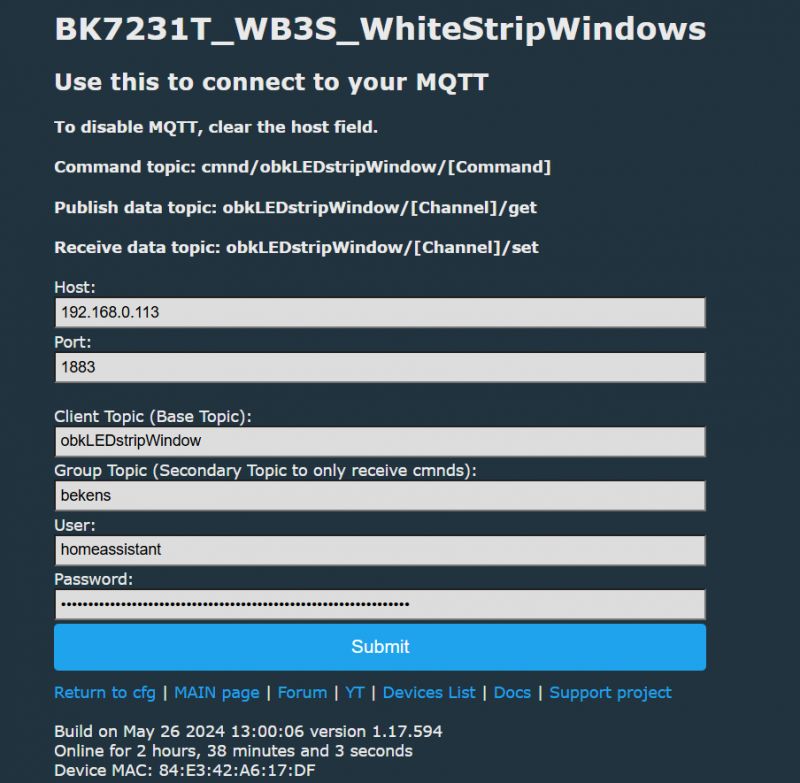
Now you can easily use it to configure your other devices, for example, OpenBeken.
That's how you can recover your MQTT Mosquitto password now! I hope you've found it helpful. I must admit, that change has taken me a bit by suprise, I didn't expect HA team to hide this password suddenly, as it was visible in the Re-configure menu for years.... strange, but least we know how to recover it.
Cool? Ranking DIY Helpful post? Buy me a coffee.






