BK7231T
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.13.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.14.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.15.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.16.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.17.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.18.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.19.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.20.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.21.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.22.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.23.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231t_1.0.24.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231t_1.1.0.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231t_1.1.1.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231t_1.1.2.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231t_1.1.3.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231t_1.1.4.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231t_1.1.5.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231t_1.1.6.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231t_1.1.9.zip
BK7231N
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_0.0.1.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_0.0.2.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_0.0.3.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_0.0.4.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_0.0.6.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_0.0.7.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_0.0.8.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_0.0.9.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.10.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.11.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.13.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.14.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.15.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.16.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.17.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.18.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.19.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.20.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.21.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.23.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.24.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.25.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.27.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.28.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.29.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.30.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.31.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/bk7231n_0.0.33.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_1.0.3.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_1.2.1.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_1.2.2.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_1.2.4.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_1.2.5.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_1.2.6.zip
https://airtake-public-data-1254153901.cos.ap...oud.com/smart/embed/pruduct/bk7231n_1.2.8.zip
BK7231NL
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/BK7231NL_0.0.2.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/BK7231NL_0.0.3.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/BK7231NL_0.0.4.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/BK7231NL_0.0.5.zip
https://airtake-public-data-1254153901.cos.ap...ud.com/smart/embed/pruduct/BK7231NL_0.0.6.zip
Beken T2
https://airtake-public-data-1254153901.cos.ap...myqcloud.com/smart/embed/pruduct/t2_1.4.0.zip
RTL8710BN
https://airtake-public-data-1254153901.cos.ap....com/smart/embed/pruduct/rtl8710bn_1.0.18.zip
https://airtake-public-data-1254153901.cos.ap....com/smart/embed/pruduct/rtl8710bn_1.0.19.zip
https://airtake-public-data-1254153901.cos.ap....com/smart/embed/pruduct/rtl8710bn_1.0.20.zip
https://airtake-public-data-1254153901.cos.ap....com/smart/embed/pruduct/rtl8710bn_1.0.21.zip
https://airtake-public-data-1254153901.cos.ap....com/smart/embed/pruduct/rtl8710bn_1.0.22.zip
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8710bn_2.0.0.zip
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8710bn_2.0.1.zip
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8710bn_2.0.4.zip
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8710bn_2.0.5.zip
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8710bn_2.0.6.zip
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8710bn_2.0.7.zip
RTL8720CF
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_2.0.0.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_2.3.0.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_2.3.1.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_2.3.2.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_2.3.3.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_2.3.4.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_2.3.5.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_2.3.7.zip
https://airtake-public-data-1254153901.cos.ap...mart/embed/pruduct/rtl8720cf_ameba_2.3.11.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_3.1.0.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_3.1.1.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cf_ameba_3.6.1.zip
RTL8720CM
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cm_ameba_0.0.1.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cm_ameba_0.0.2.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cm_ameba_0.0.3.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cm_ameba_0.0.5.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cm_ameba_0.0.6.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/rtl8720cm_ameba_0.0.9.zip
https://airtake-public-data-1254153901.cos.ap...mart/embed/pruduct/rtl8720cm_ameba_0.0.10.zip
https://airtake-public-data-1254153901.cos.ap...mart/embed/pruduct/rtl8720cm_ameba_0.0.11.zip
RTL8721CS
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8721cs_0.0.1.zip
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8721cs_0.0.2.zip
https://airtake-public-data-1254153901.cos.ap...d.com/smart/embed/pruduct/rtl8721cs_0.0.8.zip
https://airtake-public-data-1254153901.cos.ap....com/smart/embed/pruduct/rtl8721cs_0.0.10.zip
RTL8720DN
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/test_rtl8720dn_1.0.64.zip
https://airtake-public-data-1254153901.cos.ap...smart/embed/pruduct/test_rtl8720dn_1.0.65.zip
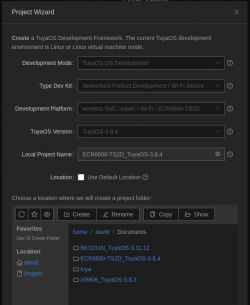
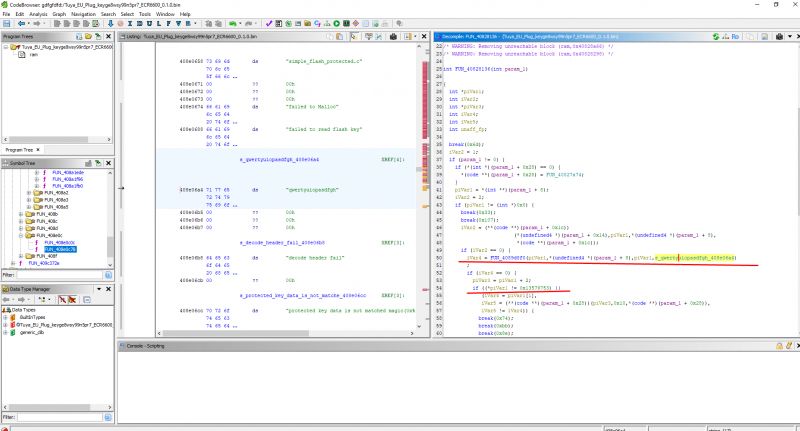
ESWIN ECR6600-TS2D (AXY)
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_0.0.1.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_0.0.4.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_0.0.5.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_0.0.6.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_0.0.8.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_0.0.9.zip
https://airtake-public-data-1254153901.cos.ap.../smart/embed/pruduct/eswin_ecr6600_0.0.10.zip
https://airtake-public-data-1254153901.cos.ap.../smart/embed/pruduct/eswin_ecr6600_0.0.11.zip
https://airtake-public-data-1254153901.cos.ap.../smart/embed/pruduct/eswin_ecr6600_0.0.12.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.0.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.1.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.2.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.3.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.4.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.5.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.6.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.7.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/eswin_ecr6600_1.0.8.zip
https://airtake-public-data-1254153901.cos.ap.../smart/embed/pruduct/eswin_ecr6600_1.0.10.zip
EFR32 Zigbee
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/efr32_zigbee_0.0.3.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/efr32_zigbee_0.0.4.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/efr32_zigbee_0.0.5.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/efr32_zigbee_0.0.6.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/efr32_zigbee_0.0.7.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/efr32_zigbee_0.0.8.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/efr32_zigbee_0.0.9.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/efr32_zigbee_0.0.10.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/efr32_zigbee_0.0.11.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/efr32_zigbee_0.0.12.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/efr32_zigbee_0.0.15.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/efr32_zigbee_0.0.16.zip
https://airtake-public-data-1254153901.cos.ap...m/smart/embed/pruduct/efr32_zigbee_0.0.17.zip
https://airtake-public-data-1254153901.cos.ap...uduct/tuyaos_demo_zg_door_sensor_0.0.5.tar.gz
https://airtake-public-data-1254153901.cos.ap...ed/pruduct/tuyaos_demo_zg_light2_0.0.8.tar.gz
TLSR825x (BT3L)
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/tlsr825x_ble_0.0.1.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/tlsr825x_ble_0.0.2.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/tlsr825x_ble_0.0.3.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/tlsr825x_ble_0.0.4.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/tlsr825x_ble_0.0.5.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/tlsr825x_ble_0.0.6.zip
https://airtake-public-data-1254153901.cos.ap...om/smart/embed/pruduct/tlsr825x_ble_0.0.7.zip
https://airtake-public-data-1254153901.cos.ap...uduct/tuyaos_demo_ble_peripheral_0.1.0.tar.gz
XR809
https://airtake-public-data-1254153901.cos.ap...cloud.com/smart/embed/pruduct/xr806_0.0.1.zip
https://airtake-public-data-1254153901.cos.ap...cloud.com/smart/embed/pruduct/xr806_0.0.2.zip
https://airtake-public-data-1254153901.cos.ap...bed/pruduct/tuyaos_demo_lite_app_0.0.4.tar.gz
LN882H
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/ln882h_0.0.1.zip
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/ln882h_0.0.2.zip
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/ln882h_0.0.3.zip
rk3308
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/rk3308_0.0.3.zip
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/rk3308_0.0.4.zip
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/rk3308_0.0.6.zip
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/rk3308_0.0.7.zip
ssd201
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/ssd201_0.0.1.zip
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/ssd201_0.0.2.zip
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/ssd201_0.0.3.zip
https://airtake-public-data-1254153901.cos.ap...loud.com/smart/embed/pruduct/ssd201_0.0.4.zip
Misc
https://airtake-public-data-1254153901.cos.ap...bed/pruduct/tuyaos_demo_examples_0.0.3.tar.gz
https://airtake-public-data-1254153901.cos.ap...d/pruduct/tuyaos_demo_quickstart_0.0.1.tar.gz
https://airtake-public-data-1254153901.cos.ap...d/pruduct/tuyaos_demo_quickstart_0.0.2.tar.gz
https://airtake-public-data-1254153901.cos.ap...d/pruduct/tuyaos_demo_quickstart_0.0.3.tar.gz
https://airtake-public-data-1254153901.cos.ap...d/pruduct/tuyaos_demo_quickstart_0.0.5.tar.gz
https://airtake-public-data-1254153901.cos.ap...d/pruduct/tuyaos_demo_quickstart_0.0.6.tar.gz
https://airtake-public-data-1254153901.cos.ap...d/pruduct/tuyaos_demo_quickstart_0.0.7.tar.gz
https://airtake-public-data-1254153901.cos.ap.../pruduct/tuyaos_demo_quickstart_0.0.11.tar.gz
https://airtake-public-data-1254153901.cos.ap.../pruduct/tuyaos_demo_quickstart_0.0.12.tar.gz
https://airtake-public-data-1254153901.cos.ap.../pruduct/tuyaos_demo_quickstart_0.0.13.tar.gz
https://airtake-public-data-1254153901.cos.ap.../pruduct/tuyaos_demo_quickstart_0.0.14.tar.gz
https://airtake-public-data-1254153901.cos.ap.../pruduct/tuyaos_demo_quickstart_0.0.15.tar.gz
https://airtake-public-data-1254153901.cos.ap.../pruduct/tuyaos_demo_quickstart_0.0.16.tar.gz
https://airtake-public-data-1254153901.cos.ap.../pruduct/tuyaos_demo_quickstart_0.0.17.tar.gz
https://airtake-public-data-1254153901.cos.ap.../pruduct/tuyaos_demo_quickstart_0.0.18.tar.gz
https://airtake-public-data-1254153901.cos.ap...aos_pixel_driver_demo_quickstart_0.0.1.tar.gz
https://airtake-public-data-1254153901.cos.ap.../tuyaos_ele_energy_demo_quickstart_0.1.tar.gz
https://airtake-public-data-1254153901.cos.ap...embed/pruduct/tuyaos_demo_examples_0.7.tar.gz
https://airtake-public-data-1254153901.cos.ap...os_dimmer_driver_demo_quickstart_0.0.1.tar.gz
https://airtake-public-data-1254153901.cos.ap...uyaos_sensor_hub_demo_quickstart_0.0.1.tar.gz